Intro
Supply chain security has never been more critical. The recent malicious Axios package — a JavaScript library downloaded over 100 million times a week — demonstrated the scale of disruption a single compromised dependency can cause. Fortunately, there are practical steps you can take to protect yourself. In this post, I’ll walk through implementing Aikido Safe-Chain both locally and in your Azure DevOps pipelines.
Stop Firefighting. Start Preventing
Traditionally, security scanning happened late — during QA, pen testing, or worst case, after a breach in production. Shift-left moves those checks to where you write code, not where you run it. You can take steps both locally and in your CI/CD pipelines to catch vulnerabilities before they get anywhere near production.
What is Aikido?
There are several tools available for supply chain security, but in this post I’m focusing on Aikido. Aikido is a developer-first security platform that scans your code, dependencies, and infrastructure for vulnerabilities.
Aikido Safe-Chain
Safe-Chain sits between you and your package manager — such as npm — checking every download in real time before it hits your machine or runs in a pipeline. If a compromised package is detected, it blocks the install. It also quarantines packages less than 48 hours old by default, giving public vulnerability databases time to catch up. This helps prevent things like the recent Axios incident affecting you.
Implementing
As mentioned, you can implement Safe-Chain both locally and in your pipeline. I’ll walk through both setups below.
Locally
Step 1. Install via terminalnpm install -g @aikidosec/safe-chain
Step 2. Set-up Shell Integration
safe-chain setup
Step 3. Restart Terminal
Step 4. Verify the Installation
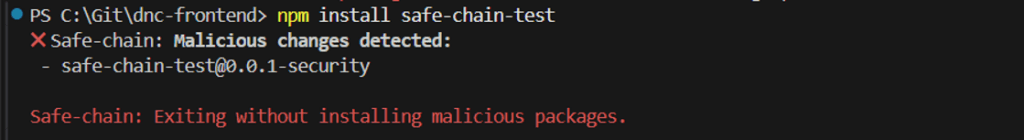
npm install safe-chain-test
When its installed and working correctly you should see output like this in the terminal:
CI/CD – Azure pipelines in this case
In order to set up in your azure pipeline you add the set-up and test (temporarily to verify) as per below:

When its set-up and working in the pipeline you should expect to see a result like below, and when this is confirmed you can remove the safe-chain-test part of the script.

Conclusion
Hopefully, this has demonstrated some simple steps that you can take in order to introduce security into your local and CI/CD at an earlier point “shift left”, moving to prevention instead of reaction.
